Trusted Computing Platforms: TPM2.0 in Context: Proudler, Graeme, Chen, Liqun, Dalton, Chris: 9783319087436: Amazon.com: Books

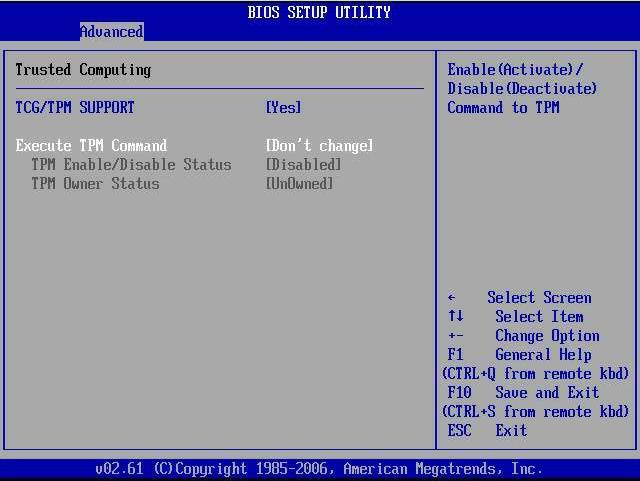
Trusted Computing Group Releases TPM 2.0 Specification for Improved Platform and Device Security | Business Wire

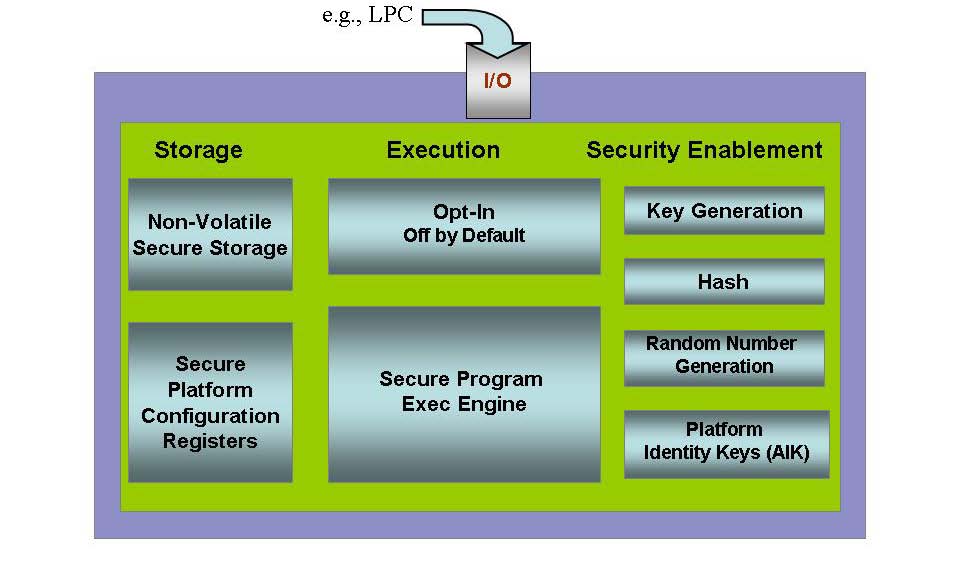
Benefits of Using Trusted Computing Technology | Trusted Computing Platforms, the Next Security Solution | InformIT

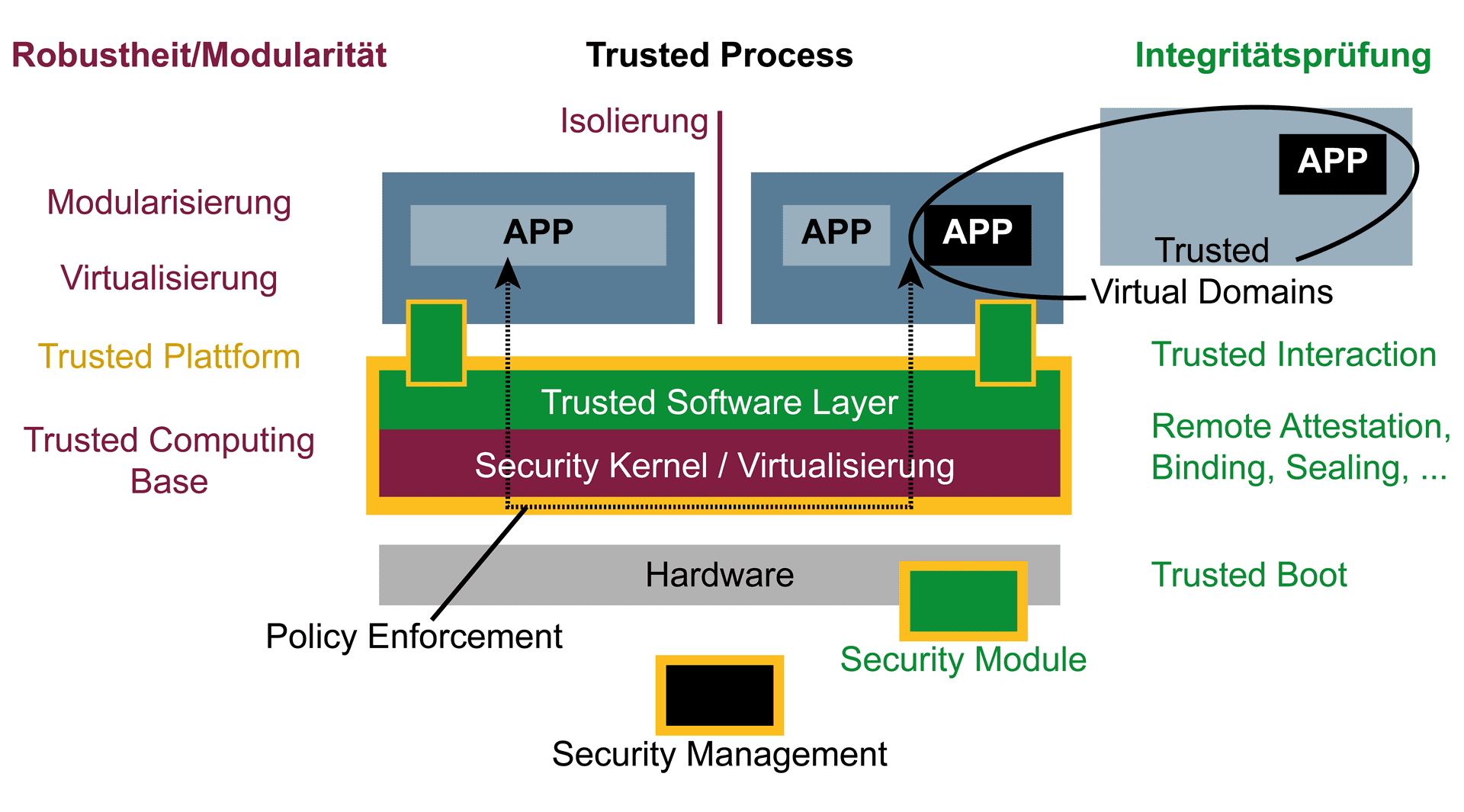
European Centre for IT-Security ( eurobits ) 1 European Multilateral Secure Computing Base Open Trusted Computing for You and | Semantic Scholar
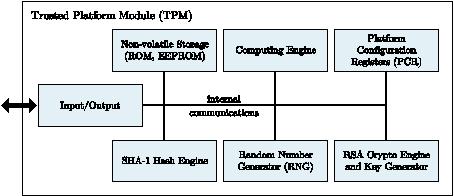
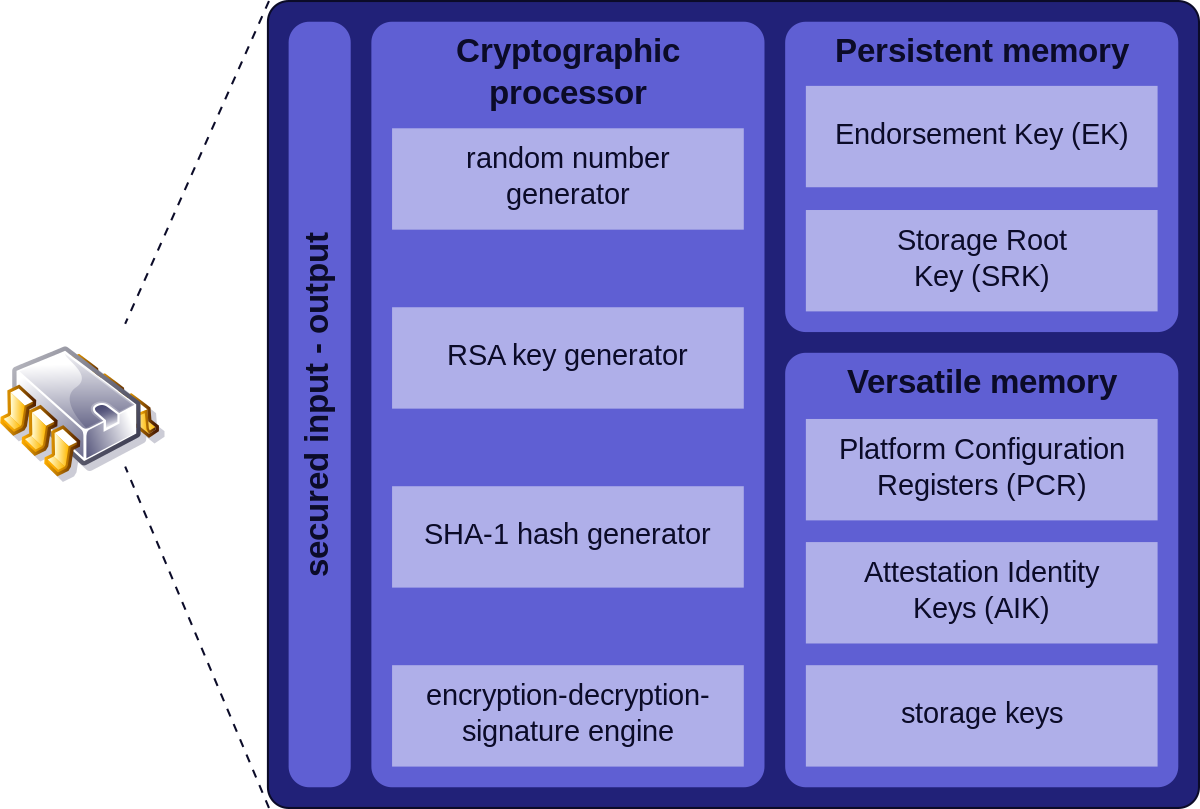
D3.9: Study on the Impact of Trusted Computing on Identity and Identity Management: Future of IDentity in the Information Society
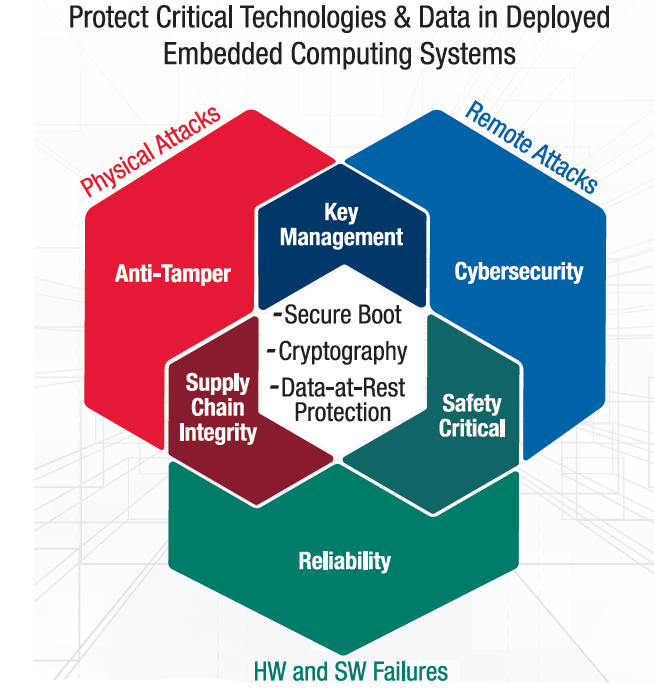
COTS-Based Trusted Computing: Getting Started in Next-Generation Mission-Critical Electronics | Curtiss-Wright Defense Solutions

The Core Concept of Access Control by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu
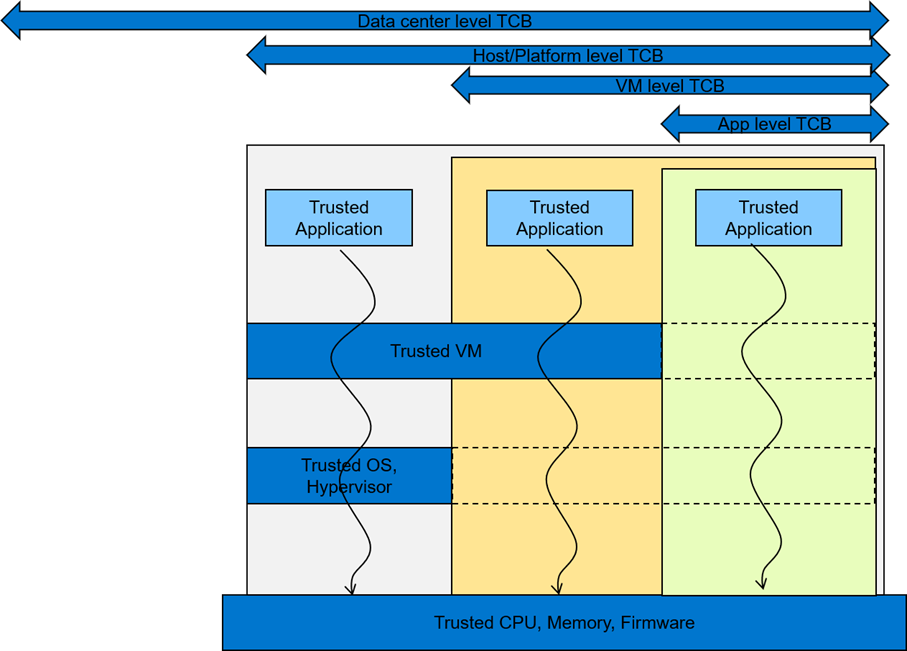
Understanding Confidential Computing with Trusted Execution Environments and Trusted Computing Base models | Dell Technologies Info Hub