Attacco hacker, rallentati alcuni servizi on line di Regione Fvg e aziende sanitarie - Studio Nord News
Vettoriale Stock Hacker One line drawing of anonymous face character. Portrait close up of a criminal with single continuous lineart isolated on white background. | Adobe Stock
Hacker outline vector icon. Thin line black hacker icon, flat vector simple element illustration from editable internet security concept isolated on w Stock Vector Image & Art - Alamy

Premium Vector | Danger theft personal data and password on computer online scam of hacker, line. fraud
Set of Hacker Related Vector Line Icons. Contains such Icons as spy, virus computer, malware, spam, firewall, computer security, password, application, steal and more. 2186275 Vector Art at Vecteezy
Hacker Thin Line Icons Internet Cyber Security Hacking And Other Icons Editable Line Stock Illustration - Download Image Now - iStock

Vettoriale Stock Computer hacker or programmer in hoodie with laptop. Man with glasses typing on computer. Internet security line style vector. Hacker person with laptop stealing personal information from internet. | Adobe

Vettoriale Stock Hacker silhouette, Computer hacker vector, sketch drawing of hacking boy, line art illustration of website hacker | Adobe Stock

Sketch of Hacker in Hood Sitting with Laptop. Internet Hacking Stock Vector - Illustration of business, hack: 129839659
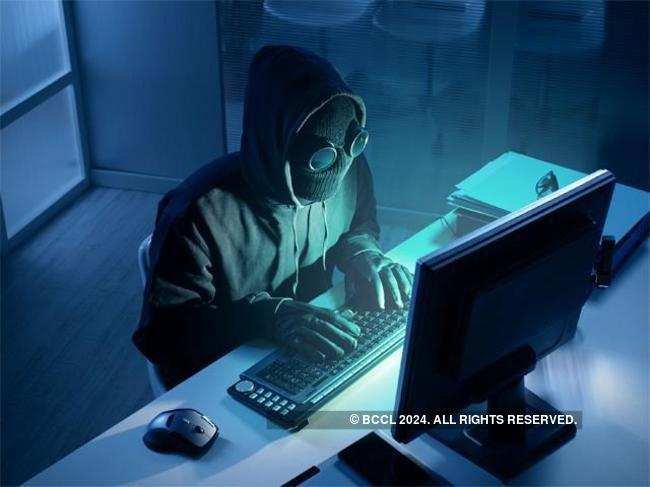
Security hacker: Your online activity is transparent to hackers: 4 new ways that expose browsing history - The Economic Times
37,200+ Computer Hacker Illustrations, Royalty-Free Vector Graphics & Clip Art - iStock | Cybersecurity, Hacker icon, Cyber attack